First steps - How to use Matrix?#
Matrix-Login#
Note
We recommend using the Element desktop client, because this avoids most problems users have with Matrix, e.g. end to end encryption.
Downloads for: Windows macOS Linux
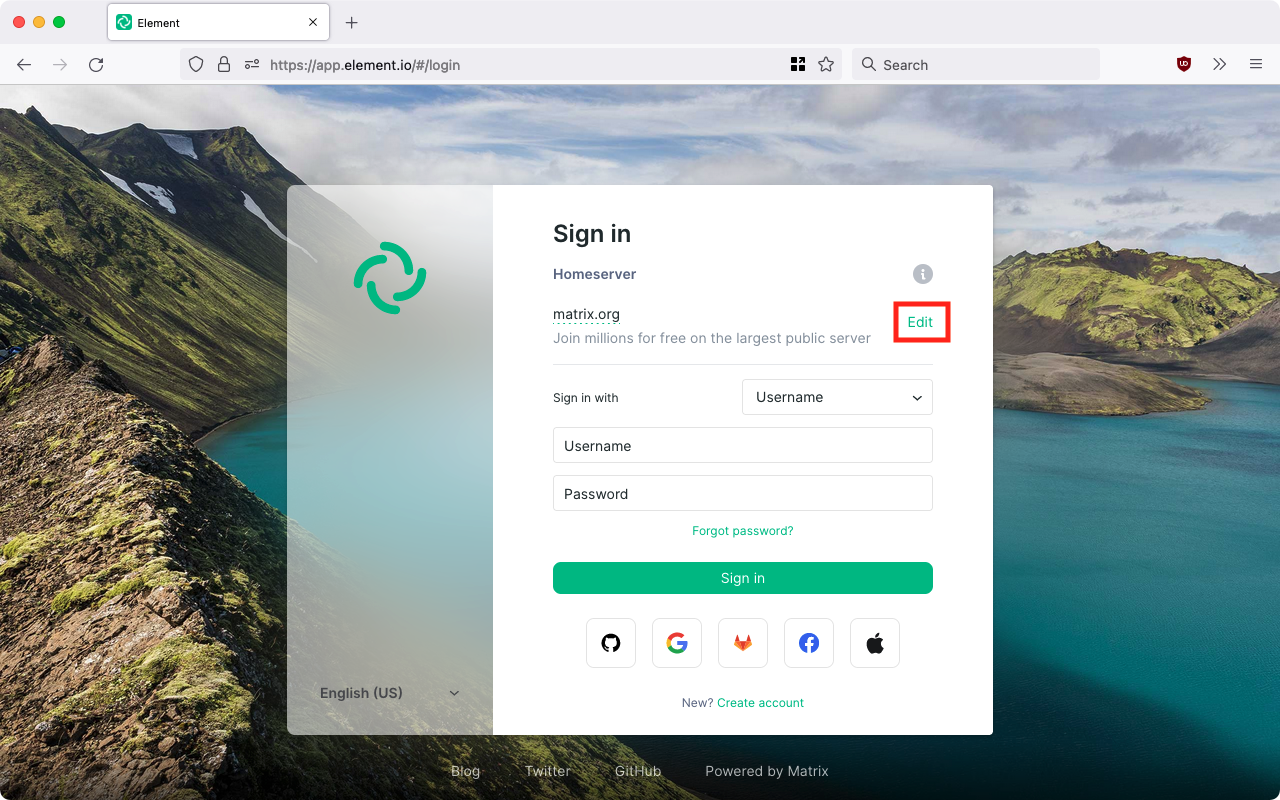
After a desktop installation, make sure to use the existing account. Here the example of Element:
This is done by clicking on Change. Then you will not accidentally end up on the wrong server...
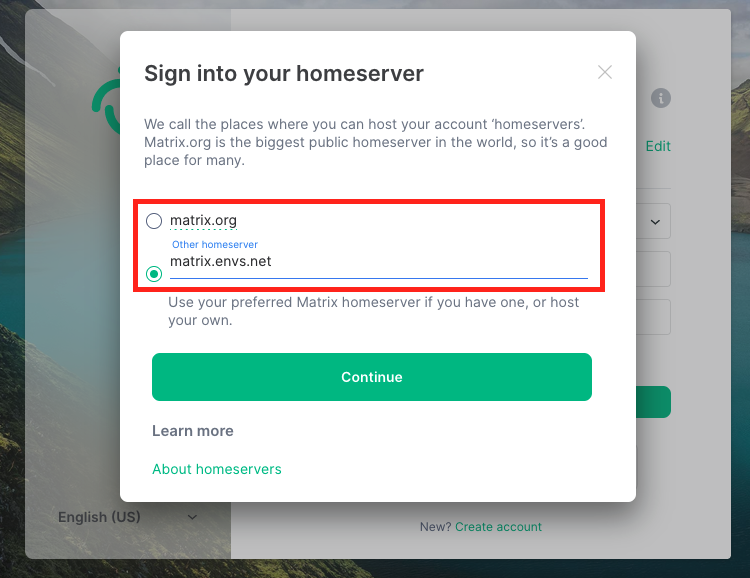
Now you can manually specify the homeserver: matrix.envs.net
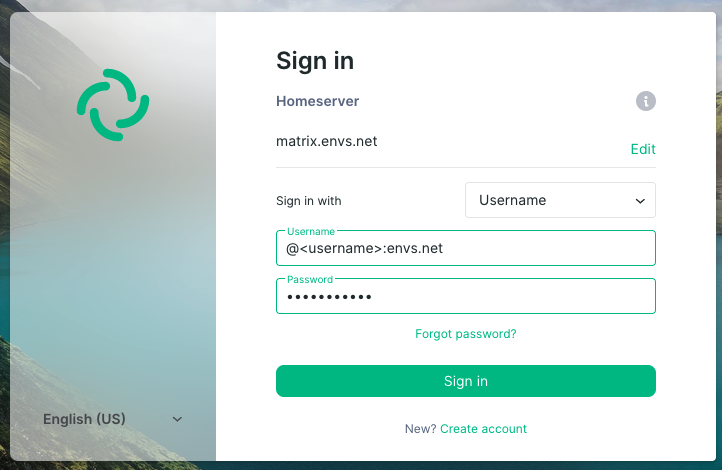
Afterwards the login with username and password must be carried out:
The drop-down menu "Log in with:" should be left at "Username". Then the following entries must be made:
Username
Enter here your username from envs.net starting with a @ sign followed by your username and the text :envs.net. For the user isabell it should like @isabell:envs.net.
Password
An alternative login, e.g. using the e-mail address, is NOT possible during the first, initial login, only after the second login.
After the first login there is also no e-mail / confirmation mail.
Analogous to e-mail addresses, this results in matrix addresses with the following structure:
@username:envs.net
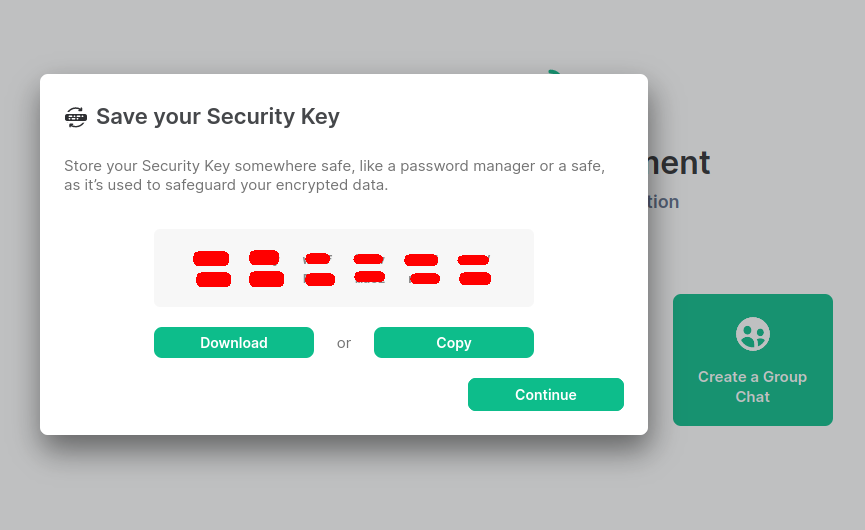
Convenient use of end-to-end encryption (E2EE)#
Matrix not only encrypts transports to and from the homeserver of envs.net but also allows the use of end-to-end encryption (E2EE). For this, cryptographic keys have to be exchanged between all devices that want to write end-to-end encrypted. This technical necessity sounds and is complicated, but in the meantime it has become very convenient for the users. The many cryptographic keys created by the client are stored on the respective device. If this is a tab in a browser, for example, there is a risk that this tab will be closed unintentionally. Then all encrypted contents are no longer readable. To prevent this from happening, a key protection is offered on the homeserver of the envs.net, on which (protected with a security phrase (or security key that can be calculated from it) all cryptographic keys are stored encrypted.
Danger
It is highly recommended to use this key backup (with a secure security phrase which is NOT your login password)!
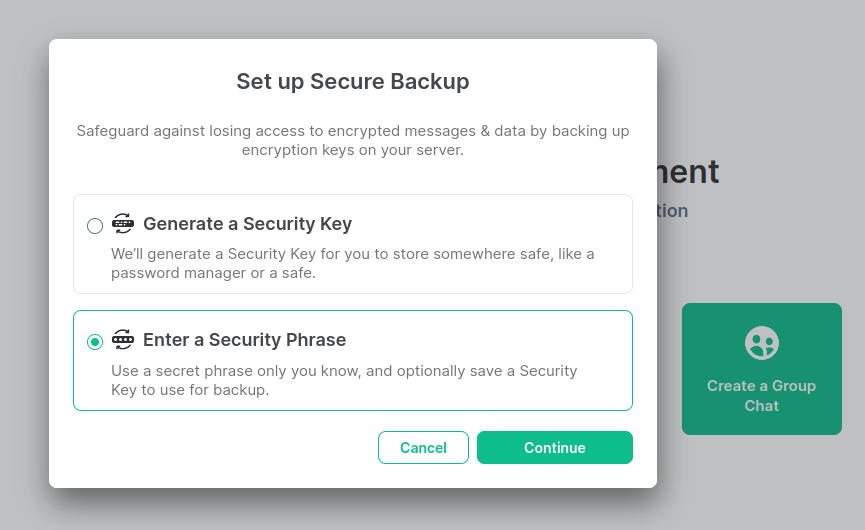
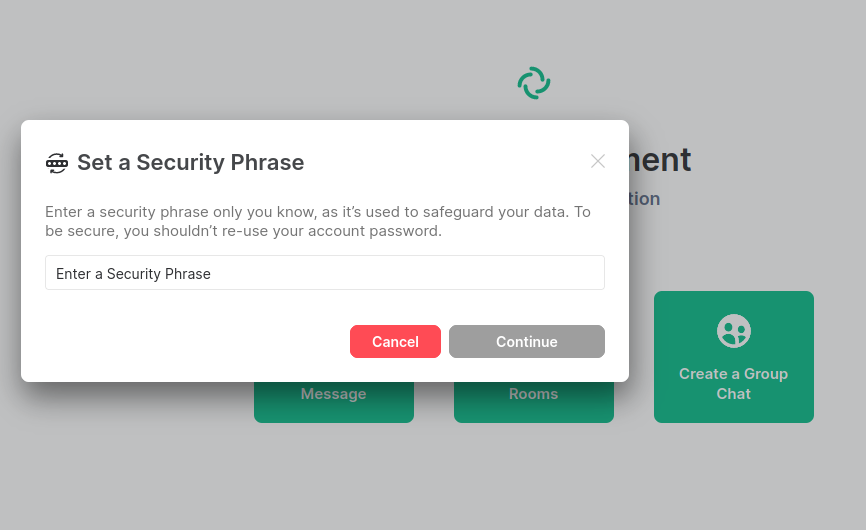 Alternatively, instead of the security phrase, you can also have a security key generated that serves the same purpose as the security phrase. Furthermore, the security key is generated in addition to the security phrase and should be kept safe and retrievable as an emergency key (e.g. save it as .txt file AND print it out)
Alternatively, instead of the security phrase, you can also have a security key generated that serves the same purpose as the security phrase. Furthermore, the security key is generated in addition to the security phrase and should be kept safe and retrievable as an emergency key (e.g. save it as .txt file AND print it out)
Other important settings may improve your Matrix experience!
Requests to setup the key backup#
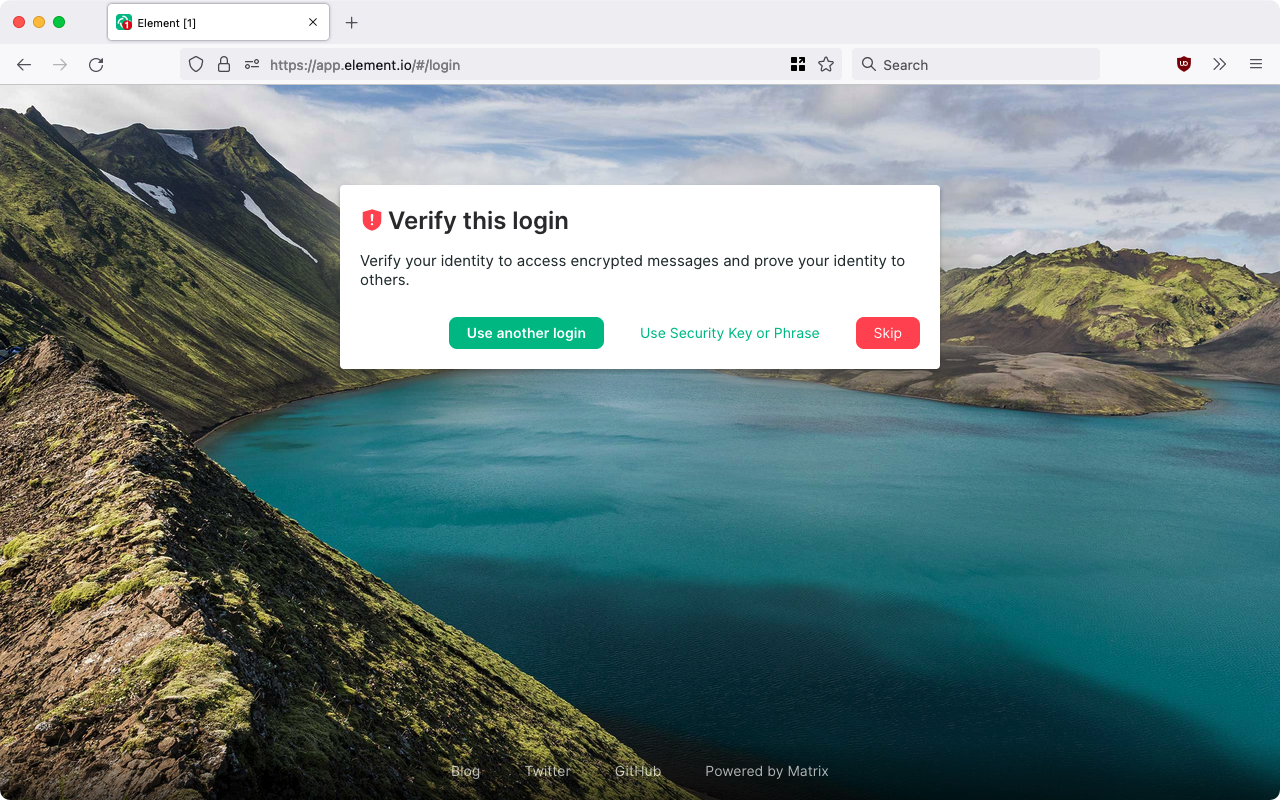
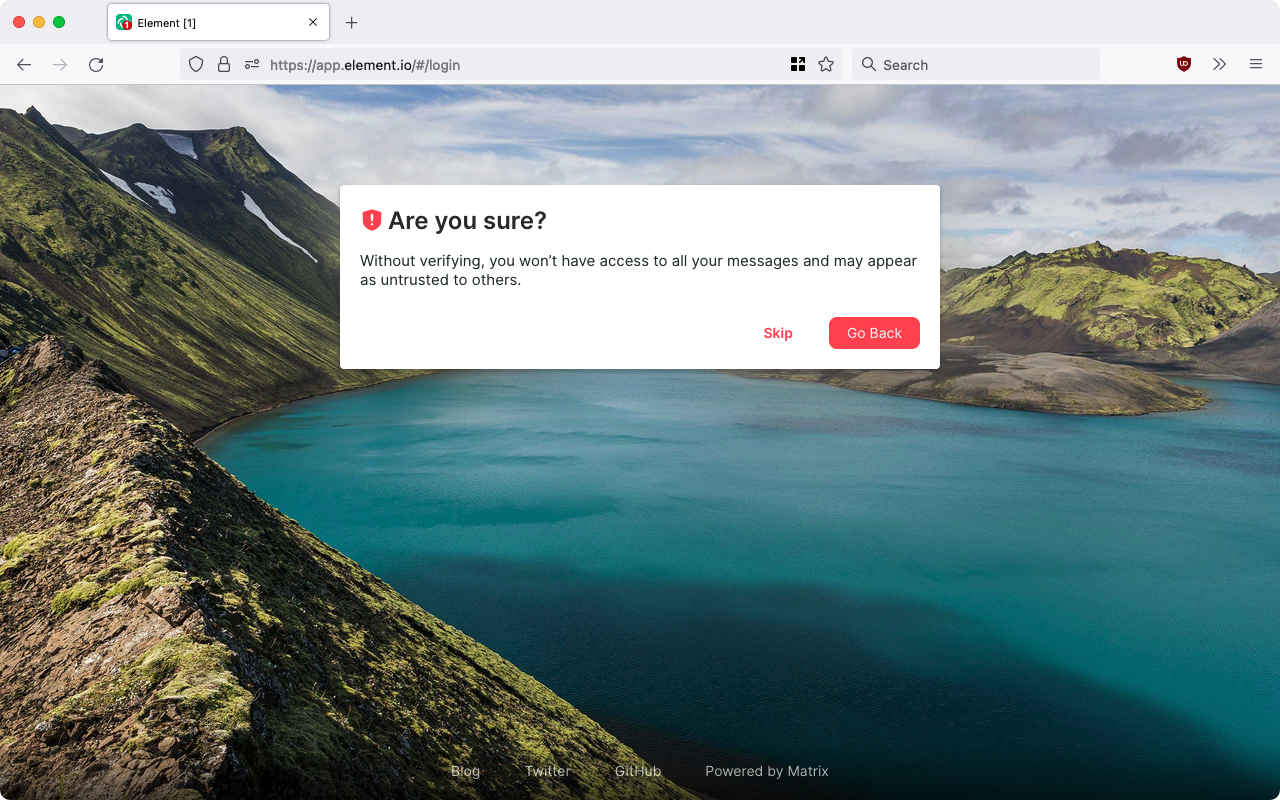
If you skipped the request to setup the key backup, the next screen would look like this:
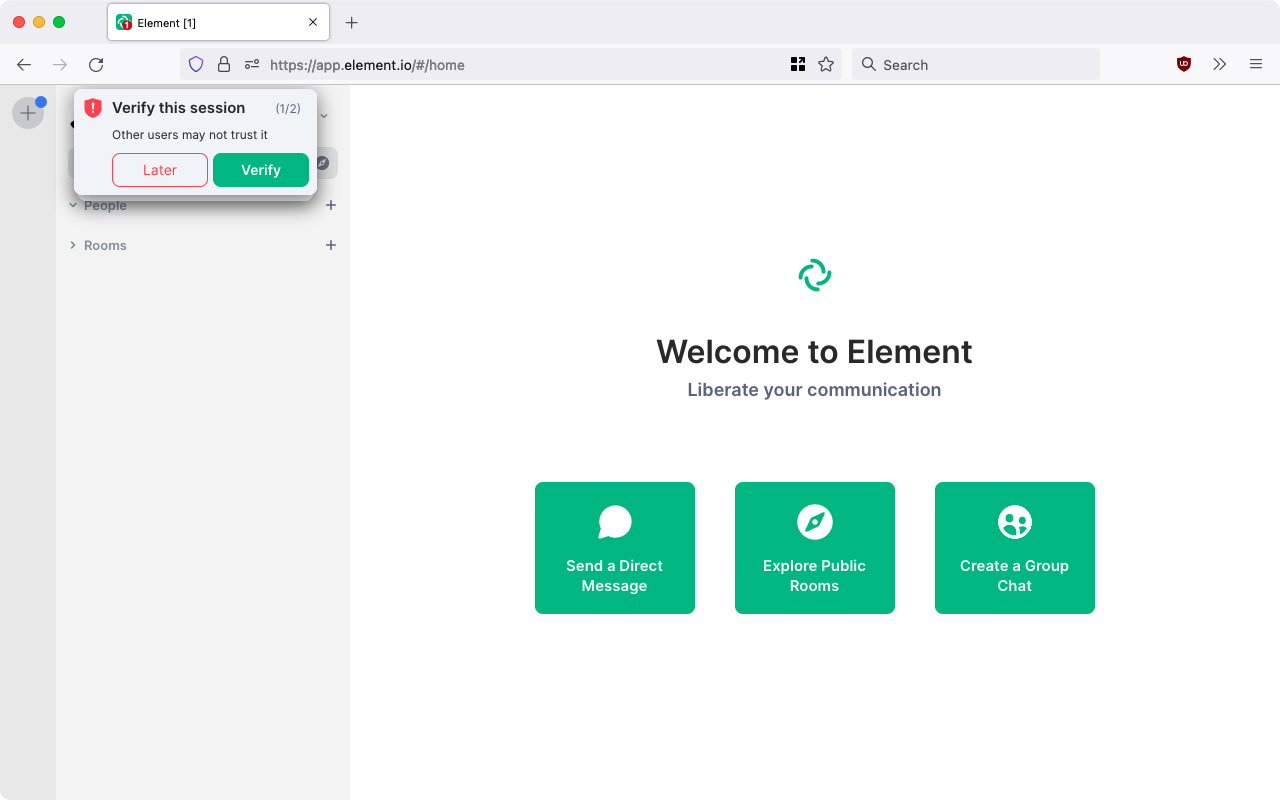
Key protection is highly recommended for worry-free end-to-end encryption. For this reason, a smaller tooltip will prompt you to set up the encryption even after you skip further:
If you omit this here as well, you will get a last warning if you log off consciously. If no key backup is set up at the latest, encrypted calls that may have already taken place cannot be accessed later. If the tab is closed, this also corresponds to a logout.
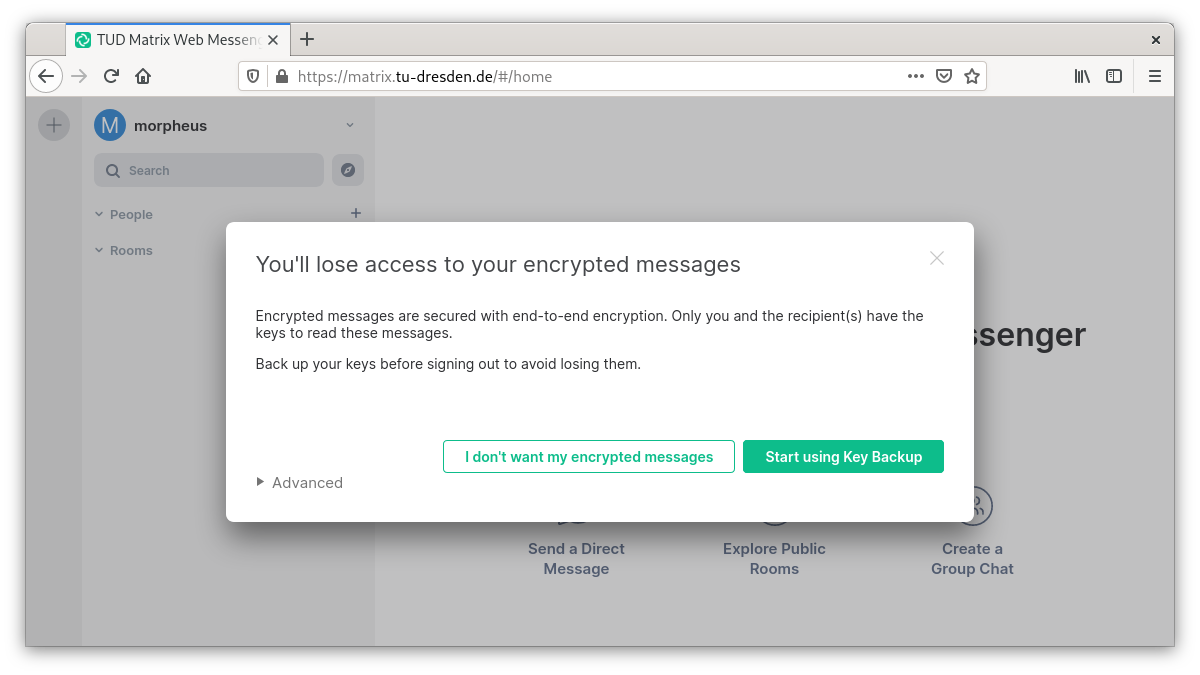
Avoid this situation by setting up a key backup!
Privacy policy#
Privacy policy: Link
Impressum#
Impressum: Link